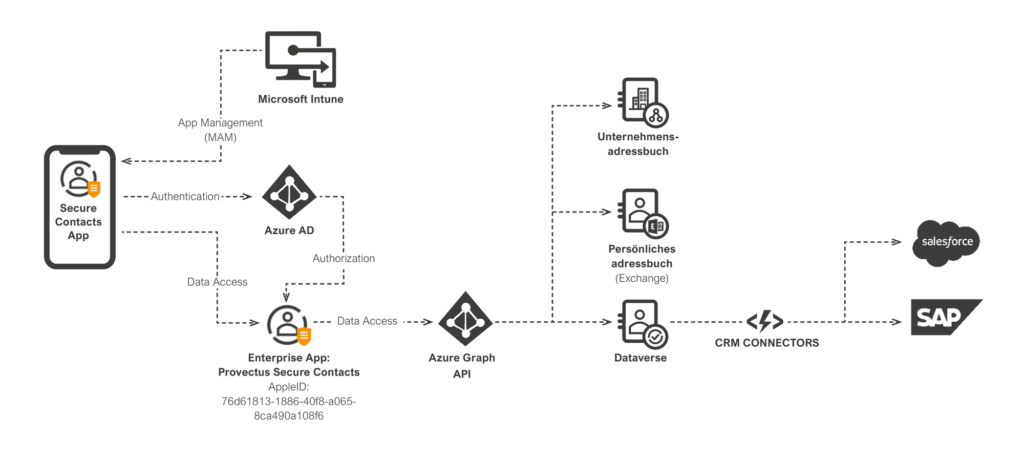
Microsoft Intune
In addition to the security features, the Secure Contacts app also integrates the Microsoft Intune SDK. This enables features to be managed via Microsoft app protection policies.
These include, but are not limited to, the following features:
- Secure access using app PIN or biometric factors
- App data encryption
- Control over data flow:
- Control of the OpenIn function: In which apps is OpenIn allowed?
- Copy/paste control: In which apps is copy/paste allowed?
- Links control: In which apps can calls, emails, chats be started and which web browser should be used?
- Access control when printing data
- Selective deletion of app data, e.g., if the device is lost
The customer configures the Microsoft app protection policies. It is up to you to decide which of these features are enabled or disabled. We only make recommendations.
Authentication
Authentication is based on the Microsoft Authentication Library. It is used to log in to the “Provectus—Secure Contacts” Microsoft Azure AD Enterprise app using a business, school, or university account. The user IDs used for login can be found in your tenant.
You configure the Azure AD user account security (password, login factors, etc.). It is up to you to decide which account security configuration to use.
Microsoft Conditional Access is used to manage which devices can use the app. This can be used, for example, to specify that the app may only be used on company-owned, MDM-managed, or privately-owned devices. The customer also configures the Microsoft Conditional Access policies. You define what types of access are allowed or not allowed.